
Server Security Tips: Best Practices to Protect Data
November 12, 2019
New Architecture Promises to Cut in Half the Energy and Physical Space Required to Store and Manage User Data
November 14, 2019On this Page:
- What Is Face Verification?
- Why Do Data Breaches Happen?
- How Is Face Verification the Savior of Databases and Datacenters?
Technology has set foot in every industry. Businesses are using revolutionary technologies to automate and simplify operations, security, employee training, fraud prevention, etc. Biometrics acclaimed global recognition and are part of complex military programs and common smartphones aswell. As per Statista, the global revenue of biometrics was $14.33 billion in 2018.
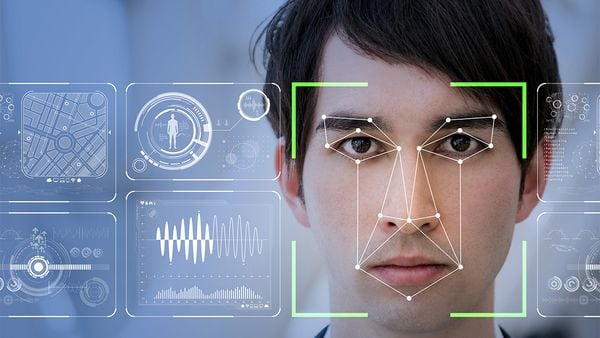
Face verification gained massive fame among the masses due to its promising features. It’s easy to integrate into the software, so programmers trust this technology for security and identity verification purposes. On the other hand, end-users also like it due to its easy usage. Selfies made face verification very easy for people to use. One of the most common usages of face verification is fraud and risk prevention.
What Is Face Verification?
Face verification is a type of biometrics that verifies a person through his face. Face verification is performed through Artificial Intelligence (AI) and completes the verification process within seconds.
First of all, the system detects a human face in the video or picture, and then it verifies the face through AI. In this verification, the person is identified through his face, that he is the person that he claims to be. In this way, the identity of a person is verified, and the risk of illegal access to any data is reduced.
Face verification technology verifies that a real person is making the verification. 3D depth perception and liveness detection verify that a fraudster does not try to perform verification through a paper-backed photo or a photoshopped image.
Several promising features of face verification and face recognition makes it a simple and easy solution to mitigate data breaches.
Why Do Data Breaches Happen?

Credit: Campus Safety Magazine
Data breaches could happen due to several reasons. Some of the significant reasons which initiated some major data breaches in history are as follows:
- Lack of security protocols in the organization is one of the major causes. The security of data centers is crucial. Security protocols should be exercised in data sharing and data access.
- Lack of employee training increases the chances of an employee falling prey to an email phishing scam. In such scams, the hackers send phishing emails to an employee with a hyperlink. The moment an employee opens the link, he gives access to the hacker to confidential data of the company.
- Internal fraud could also initiate a data breach. Sometimes employees are bribed by the hackers to give access to the databases of their company. Businesses can quickly reduce this threat by limiting common access to confidential data.
All the reasons mentioned above for data breaches are a threat to businesses, and these threats could be addressed smartly through a well-developed cybersecurity strategy and practicing strict security protocols.
How Is Face Verification the Savior of Databases and Datacenters?
Making face verification a mandatory part of data security and data access protocols could help in achieving rigid security.
Face Verification for Access to Data Centers
Recently NordVPN officially confirmed that one of their data centers became a victim of a data breach. The company had a data center in Finland that was outsourced from a data center provider. The company claimed that the data breach happened due to a weak remote management system. Some intruders gained illegal access and exposed confidential data.
Such data breaches happen due to weak security protocols at data centers. Using face verification could reduce this risk as face verification delivers the results with high accuracy, and there is no chance that a criminal could enter a data center with a photo or authorized individual.
Credit: Cisco Newsroom
ID card screening could fail here as the criminal could steal an ID card of an authorized person, but stealing someone’s face is impossible. Face verification detects minor differences as well, so even people with similar faces could not enter the databases.
Using Face Verification for Gaining Access to Technical Assets
Computers and other technical assets of a company like software, etc. could be accessed easily by employees through their systems provided by their organization. First of all, businesses should limit access to these resources to control risk. Secondly, face verification roadblocks should be added to the overall system, wherever confidential data access is involved.
Businesses that deal with massive data could not restrict the data access, so they should use it to control fraud within the company. It will reduce the risk as criminals try to commit a crime in an unnoticed manner, and face verification will verify their identity before giving them any access. It will demotivate the internal agents from committing a crime. Also, it will reduce the risk of coming from external sources. In case a criminal gains illegal access to a data set, the face verification roadblocks will mitigate risk. Such security roadblocks often demotivate hackers.
To wrap up, face verification has a huge potential of securing the databases and data centers. It’s easy to integrate quality makes it a feasible solution. In case a business doesn’t have the necessary resources to develop a face verification solution, they can outsource a facial recognition solution. The key to thorough risk prevention is to develop a foolproof cybersecurity plan, including topnotch technologies like face verification.
Main Photo Credit: Visidon

1 Comment
[…] With the increase in technology, the number of frauds has also increased. Businesses are suffering huge losses as fraudsters refine their tactics. Enterprises are leveraging natural language processing, video recognition, machine learning automation, and speech recognition for improving the detection process. […]