
Sabey Opens New York Data Center
March 21, 2013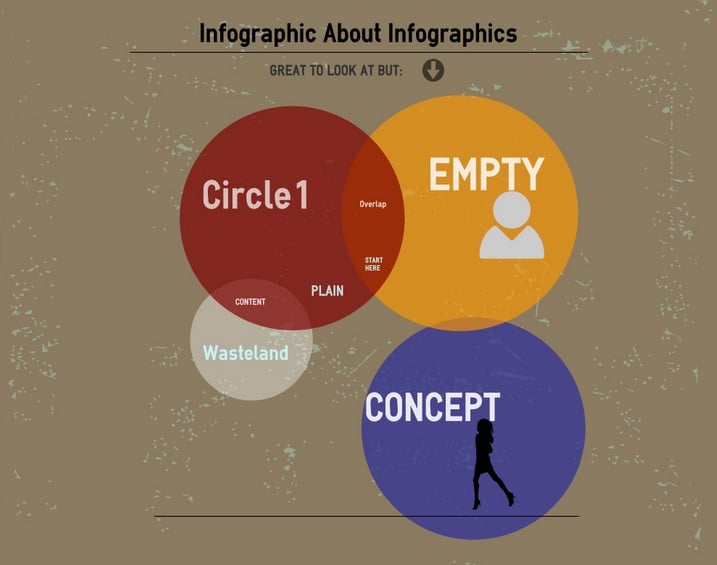
9 Apps to Create Your Own Info-graphics
March 25, 2013Cyber criminals are becoming a major threat to computer users throughout the world. Many of these criminals are very bold because they believe that they can hide behind the cloak of anonymity on the Internet.
 Cyber criminals are becoming a major threat to computer users throughout the world.
Cyber criminals are becoming a major threat to computer users throughout the world.
Many of these criminals are very bold because they believe that they can hide behind the cloak of anonymity on the Internet.
Fortunately, computer hackers are not untraceable. You can identify them and help the authorities make a case against cyber criminals if you follow a few measures.
How to Trace an IP Address
Here are a few basic guidelines to help you trace computer hackers. Keep in mind that many sophisticated computer hackers will be more cautious about tracing their steps. Many hackers use proxies or dark web sites such as Tor. They can still be traced, but doing so may be a bit more difficult. These guidelines may help you identify some hackers, but you may need the assistance of an expert to catch many in real life.
How to Trace a Hacker
You will need to identify the IP address of the intruder. There are a variety of Linux commands and tools that can tell you what the IP address is of any computer that is trying to make a connection. You can find the IP address of anyone trying to hack your own website on your hosting logs, Google Analytics or another analytics tool.You can try to use a tool such as NetStat to identify the IP addresses of anyone trying to connect to your computer.
What to do with the information: Once you have an IP address you can find out where the connection is coming from. Keep in mind that these simpler tools won’t be able to tell you exactly where they are, but can give you a reasonable idea what city they are in and what hosting provider they are using.
You can use the traceart command to find the hostname of the IP address that the hacker is using to access your machine. You can also put the IP address on the trace-route tool on the Princeton website. Another alternative is to use the GEOIPTool to get a rough idea where the hacker is located.
Reporting an IP Address Hacker
You won’t be able to track the hacker’s exact identity when you try these techniques. However, there are a couple of ways that you can use it:
– You can turn them over to the authorities.
– You can report them to their hosting provider after learning their identity.
I would suggest the former in most situations. You will know which country’s jurisdiction to contact to report the crime.

IP Hackers: How to Remain Vigilant
Some hackers are annoying pests that have too much time on their hands. Others are much more sophisticated and dangerous. You will always need to be on your guard to protect yourself.
The topics I covered above can help you learn enough about a hacker to report them to the authorities or their ISP. However, they will usually not be very effective against more sophisticated hackers who are trying to cover their tracks. You should always take the necessary steps to keep your computer safe and leave the harder work to the authorities. Above all, make sure that you don’t try to use any information you find to antagonize them. You don’t know what havoc they could wreak on your system if you aren’t so careful.
About the Author: Kalen is a technology and security writer who shares tips on identifying and stopping criminals.
30 Comments
My PC is being attacked and the Hacker has tried using LogMein to access my PC, Logmein have identified the IP Address as located in Malaysia.
Whilst I do not have Logmein on my PC right now, I have used it in the past 6 months and I assume that unless I have a user PIN then the Hacker cannot obtain access.
The Hacker has also tried to Hack into my Gmail account, but Google have thwarted this attempt and advised me to change my PW which I have carried out successfully.
Most likely that is a bot running its requests through a proxy server. The bot is probably doing brute force password sweeps and Ip sweeps in an attempt to find more hosts to inject, infect and then pull data out of.
I want to be honest with this, Hackers can never let you trace their Ip address because they are not dumb. Hackers that use Gmail account are fake hackers and I still wonder why people still use them and cry later.
Hackers always use the deep web services to list their services because you can never trace an IP address with TOR browser.
I was tricked once anyways, that was exactly what made me go into research and ended up on dark Basin forum.
You should never ever let your personal details out to hackers and that is why they always prefer BTC as the mode of payment.
Try kicking him out on cmd console
how?
I’ve seen I so many movies and in mr.robot also when a system is in cyber attack.there are so many IP’s indicated of that hacker.like from Korea,china,USA,india,Russia.
What’s that and how hacker’s manage to do that.
I let some people use my phone. After that been hacking my cell. My gmail my fb everything I have all my info. Wouldn’t surprise me the perverts watch everything I do.. What wrong with people?? How does someone track these creeps?? Anyone have someone that would work to get this traced??
no idea about tracing it.but it looks like a payload trojan on your phone.
if you are using an android phone then pls open the application manager and look for any unknown software in downloaded tab.if any found uninstall it.
Hope that might help.
My email got hacked and I’m only eleven I have the ip address do you need it to track my hacker?? He/she used my email and I’m scared they could find any of my personal information but I changed my password and I don’t know if that would help.
Tweet this to the Donald. He thinks “you have to catch them in the act”.
my rogue landlord as hacked into all my accounts..fb deleted paypal and ebay were closed she has sold my identity to developers and she seems to have the power to know my every move and i think she even goes into the house when im not there this is driving me mad can any one help me catch her
Rachel,
This sounds very serious. I would recommend contacting the police.
you know that sounds like a new profession. Hacker Police 🙂 These guys go to school and receive a degree in computer technology and then join the police force in every city in the country. like narcotics or homicide detectives. We need a new law or something.
They do have something like that, ethel. Its a 2 year associates degree called Cyber Criminal Justice, which focuses on Violations of the law via electronic means, i.e computers and hacking.
Same thing is happening to me did you get it resolved what can I do
Rachel put A CAMERA in your home!!! face it towards your front door hidden and the minute anyone enters take the recording to the police and also let them know about this person hacking (stalking) you. meanwhile have the police record it in the meantime so that they are aware of your concerns.
We definitely need hacker police. I’ve had the same jerks hacking my Wi-Fi and multiple phones for a year now. They also hacked my family’s Wi-Fi. They sit out in front of the house when no one is home and hack into the Wi-Fi…
nice
Thanks for the wonderful post information very useful guide.
Interesting information. But I have to ask you … can the source of a hack be identified with CERTAINTY if the hacker used a VPN or a PROXY or TOR? Isn’t it possible to be a hacker in Canada and make it look like the hack came from Russia? Also do you think these alleged hacks from Russia are identified with certainty? Wouldn’t you think the best hackers in Russia would assure that they could not be tracked back?
Thanks.
To track the IP address the post is very informative as the if anyone has to track any of the IP or its own IP, then the given details will be useful.
should aware always from hackers which attack of your device and get all the data need to know how to save your data in advanced technology
Nice article
My husband just found up my google account just link at MAC computer. We dont have any MAC computer. And he told me that i’ve download dating apps inside MAC computer using my gmail. Because of this issue, i have problem with my husband and he don’t trust me anymore. Please tell me… what should i do?
Anybody can help me someone try to hack my facebook accout and telegram i want to know the real location of hacker when i look my phone the ip address name is from other country name of guatemala city but i know the person who try to hack my account is only stay here in Philippines
Tracert (Windows) or traceroute (Linux/macOS) can identify the network path between your device and the target IP, potentially revealing intermediate servers.
Ethel has hit the mark as far as I am concerned. Police harassment is worse than ordinary ‘criminal/ hacking, just as state violence is far worse than the “domestic and family violence” that gets so much media attention. I can not go online without being stalked online. A long history. It’s time they got their come-uppance. Can you advise on how to document for legal attention?
How is that we send a man to the moon and we aren’t able to stop foreigners from hacking in America If the President or a Senator got hacked the FBI would trace an IP address but ordinary citizens only get to file a report and wait for years for a class action lawsuit to be settled
Quite shockingly stalkers can do this. Had a group of stalkers / hackers, and predators. One weird creepy woman hired a hacker to hack and steal emails, accounts and such. The two main culprits are located in Alabama and Baltimore. Little do they know, they are under investigation, just waiting for them to slip up.
please stay focus, most of these so called hackers here are Basterd, Now i know how good hackers work, they never advertise themselves in such a credulous manner and they are always discrete. I have been ripped off so many times so from experience I know so much on how they work…Eventually my zeal to solve my issue paid off when a friend of mine