This Week in Getting Hacked: Hilary Clinton’s Basement Edition
October 14, 2015
This Week in Getting Hacked: Can’t Stop, Won’t Stop Edition
October 21, 2015Portable Technology has changed the world. What the internet once did for users in the home, it now does for all of us, everywhere. There’s a great amount of freedom involved with this, but it’s not an unqualified good. The Taoist conception of yin and yang suggests that nothing is all good, and nothing is all bad, either.
So where is the bad? Isn’t being able to make a dinner reservation from what seems like the middle of nowhere a good thing? Shouldn’t the benefits of a search engine extend to anywhere there’s Wi-Fi service?
The answers to those questions are both yes. Once we discover all the things we can do online, with our portable devices in hand, on the wrist, or clipped to our belt, we’ll never go back to what we did before. Nor should we. But there are risks involved, too.
Hackers are Always a Threat
Putting anything online carries a risk that someone will find it and use it for their purposes, and not yours. As sophisticated as technology can be, there’s always a way for someone with tech skills and determination to get at it. Like the safe-crackers of old, modern-day hackers can size up security measures and look for ways of getting around them. And all too often, they can find them out.

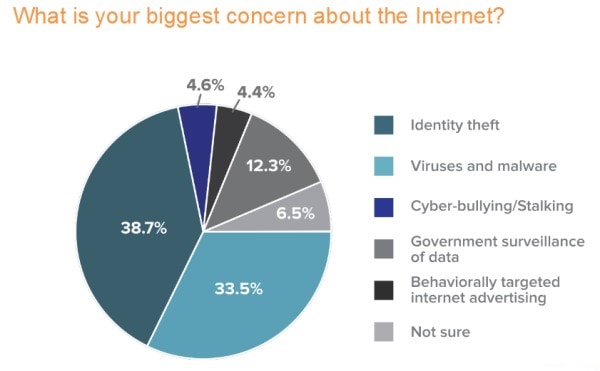
Identity theft is a soaring concern, made all the more real by the proliferation of smartphones and other web-enabled devices. Credit card information, medical history data breaches, and the likes are all risks that come with our wireless lifestyles today. The more web access that we have, the more dangers we face.
Wearing the Web, Everyday
The next step in the evolution of a cloud based phone system is wearable technology. Google’s eyeglass experiment is perhaps the most visible example of taking the internet with you at all times, but other examples are right behind it. From a wristwatch to a fitness tracker, we can now transport the internet with us, wherever we go. And those armband holders for our cell phones when we want to go running are one more example. Wherever we go, the cloud allows the internet to come with us.

But this “wear ever” revolution lets the data thieves come with us, too. We realize that our home computers need protection, but our need for protection while on the go is less understood. The protection that we need can come from the cloud, but first we have to realize what we need and how to find it.
Finding Answers in the Cloud

The cloud helped make this all possible, but it can also provide the solution to the problem. Security solutions based on cloud technology can meet the problem where it exists, and head off the type of malware and data breaches that can put private information at risk. Realizing that the cloud monitoring tools can offer real time protection services, in addition to the greater flexibility and portability that we already know about, can be a tremendous relief. But only if we realize the dangers and plan for them accordingly.The global nature and reach of the internet is a glorious thing, but it carries a risk that we must also be aware of. Our online presence is worthy of protection, because being a Luddite is not a viable option. Embracing the cloud and all of the possibilities it offers is a must, but so is protecting ourselves in the process.
Think of it like this: Would you get into a car and not put your seatbelt on? Of course not, but people once did this all the time, many years ago, because the need for seat belts wasn’t fully understood. While the automobile was first introduced in the late 1800s, the first modern seatbelt, as we know them, was introduced in 1959. How many lives were lost in the half century where people simply did not understand the need to restrain themselves in the event of a crash?
The need for security online may not literally be a matter of life and death, but it can have far-reaching consequences. And being unaware of the dangers out there is not acceptable. It’s much better to realize the risks, and take whatever steps are available to head them off, before it’s too late.
As the technology of the internet continues to expand, there’s an understandable need to jump into the fray ourselves. Who doesn’t want to be a step ahead of their friends, when it comes to the latest mobile technology? But doing so won’t be a headlong rush into an unforgiving online abyss, either. Embracing the cloud as a source for greater capabilities, and for greater security and protection as well, is to realize the true yin and yang of online technology.
Author Bio:
Sheza Gary has been a Project Strategist since 2009 and also involved in the launching of startups and tech companies in New York for over 5 years. She has keen interest in writing her own experiences about business plans and upcoming business supporting technologies. You can also follow me on Twitter @shezagary