
What is Virtualization?
December 19, 2019
5 Reasons your Small Business Needs Efficient Cloud Storage Solutions
January 2, 2020Data and the need to protect it have become more critical now more than ever. In the last couple of years, we’ve heard companies, some quite prominent, engulfed in data breach scandals. As an organization, business, or individual, you might be afraid of embracing new technologies in data management and storage because of security systems.
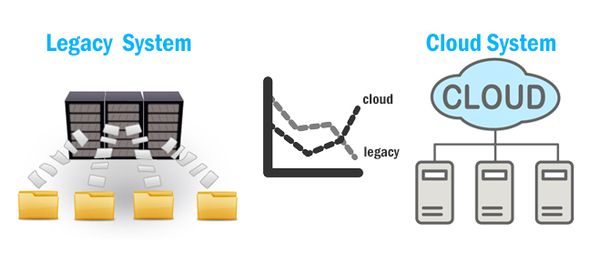
And therefore, you choose to trust legacy systems. But clinging to that old technology may have your business stuck in a rut and hindering growth.
So, how do you manage your data in this new age? One of the most popular methods is the cloud. According to the 2018 State of the Cloud Survey, 81% of enterprises have a multi-cloud strategy. The cloud is easy to use, cost-effective and offers long-term archiving and retention.
However, even though the cloud has gone mainstream, there are still concerns among businesses, IT leaders, and consumers about how secure it is. It may surprise you to hear that cloud storage solutions are actually more secure than legacy systems. Here’s are five reasons that prove this point:
Cloud Systems Are Always Kept up to Date
Just from the definition, a legacy system is outdated. It does everything it was created to do. However, it has no room for growth and cannot, therefore, adapt to the increased level of the current cyber risk.
However, even if you do want to keep your legacy system up to date, it is much more challenging to accomplish as you will need to check hundreds of computers and update their systems. As a result, most on-premises systems tend to fall behind.
As technology advances, you want a data management system that is relevant to the times – secure and the one leveraging scalability vs elasticity. Public cloud solutions such as Microsoft Azure, Amazon Web Services, Rackspace, and Google Cloud, are continually updated with the newest security features.
These giant providers possess the financial resources, cybersecurity teams, as well as invested interests to ensure they are always ahead of hackers. So, when you choose to switch to the cloud, you can rest assured the team behind the service is working towards improving the security of the servers your data is stored in.
Cloud Centers Have Multi-Layered Security Measures
Legacy systems can be unreliable. And since these systems were developed before cybercrime became as sophisticated as it is today, controlling access to computers on-premises with as simple a method as lock and key were all that it took to keep out hackers.
Now, if you rely on a legacy system alone, you risk getting remote attacks from hackers. Most businesses that still use these outdated systems use them along with the cloud (mainly as backup). But even with this approach, your data is still pretty much vulnerable.
On the other hand, data centers, managed by cloud service providers, employ a multi-layered security approach to mitigate threats before they materialize into serious cyber-attacks. These usually involve a combination of physical measures such as patrol guards, barbed/ electric wires, tall fences, surveillance cameras, etc.
The cloud user then fortifies this protection by setting up strong passwords and authentication. That is why, in most cases when data breaches have occurred, it is usually an individual’s credentials that have been stolen.
Cloud Systems Have Lower Risk of Human Interference
According to recent statistics, 95% of cybersecurity breaches occur due to human error. Legacy systems are usually on-site. That means you will need to invest in various security measures to prevent staff, visitors, and any unauthorized persons from accessing the machines that are holding your company’s data.
On the cloud, however, your data is stored off-premises in a data center. This place is not accessible to people. With this physical restriction, it is much harder for unauthorized persons to stumbling upon your sensitive company information and use it to your detriment.
Cloud Service Vendors Are Expected to Undergo Audits Annually
Cloud vendors must go through rigorous audits every year. These audits are there to prevent anomalies or breaches in security systems. This measure keeps data centers working optimally and ensures that problems are identified early.
On the other side, legacy systems rarely, if ever, get audited as it is not mandatory for them. In most cases, on-premises systems can go for years with just one audit. This laxity creates room for security discrepancies.
Cloud Systems Are Monitored
The cloud vendor’s main job is to keep their clients’ data safe. Therefore, they must monitor their infrastructure closely with no breaks. If a potential issue or threat arises, it is flagged and addressed immediately. But if you keep your data on your on-premises infrastructure, it is almost impossible to monitor it at all times.
Apart from the costs involved, you would also have to hire a specialized cybersecurity team to take care of any cyber-related issues that may occur. The cloud offers highly secure data storage as well as skilled IT professional support. And a fraction of the cost you would use storing the data yourself.
Final Words: Switching from a Legacy System to the Cloud
To sum it up, most worries about security when you switch to the cloud are brought about by misconceptions. As long as you are storing your data in a third-party server, you still have full control over it. Only you can access, change, or remove it.
Additionally, you hand over the costs and responsibilities of providing physical security for the data systems to the cloud service provider. And since CSPs are specialized in the services they offer, they provide better protection for your data than any other organization.
Now, new technologies such as the Internet of Things, Big Data, and Artificial Intelligence are working together with the cloud to make it even more convenient, efficient, and secure. Remember to perform due diligence as you move your data from your legacy system to the cloud. First, plan and then – deploy.
1 Comment
I completely agree that the cloud is much more secure than legacy system. Of course, there are some doubts. For example, scenarios when an internet connection will be lost. But in terms of security cloud systems are far more superior to anything we saw before.