
How Data Center Design Is Becoming More Resilient for Smoother Data Transfer
August 1, 2019
3 Creative Ways the Tech World Is Striving for Sustainability
August 7, 2019Network segmentation can improve network security, but it’s not a small project. Here is what it means to segment your network as part of an in-depth defense strategy that will improve the cybersecurity posture of your organization.
Why Network Segmentation?
Traditional networks are usually structured to have a rigid outer shell while remaining soft on the inside. This is to keep external attacks at bay, and as such, most regulated networks have a full-proof firewall perimeter with some Intrusion Prevention System (IPS) that monitors traffic coming into the network.
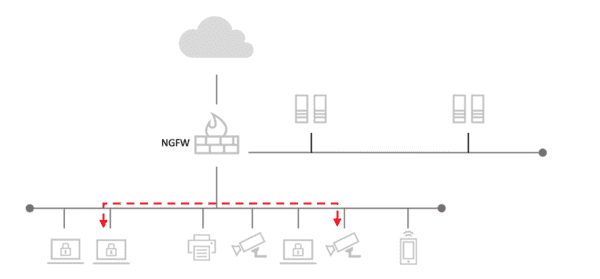
However, if attackers can get past the firewall perimeter, they will access the network’s soft insides and cause damage. Unsegmented networks usually have a flat internal structure, and this means that once you are within the network, you can easily access all the resources within the network. Such networks are also externally focused, and this means that intruders who have managed to penetrate the firewall will not face any opposition as they go about their activities within the network.
With networks exposed to more attacks than before, network segmentation creates internal barriers within networks, and this makes it difficult for intruders to penetrate the whole network and cause damage. It also isolates sensitive data and information systems from curious insiders, and this ensures that your vital business information does not fall into the wrong hands.
What Is Network Segmentation?
From the brief above, network segmentation is the process of splitting a computer network into smaller segments. This way, you are separating groups of users, applications, and systems from each other to ensure better network security and to protect sensitive company data.

The traditional flat network infrastructure has all the servers and workstations on one local network (LAN). This infrastructure is not always ideal since you may have devices and systems that don’t necessarily have to interact and communicate with each other. Putting such systems in one local network provides intruders with the opportunity to access the entire network since all they have to do is hack into one system that gives them access to the whole network.
By splitting the network into small groups, network segmentation makes it difficult for hackers to access their entire network from one point and cause damage. It limits communication and interactions within your network, and this reduces the attacking options available to intruders. Network segmentation can be implemented virtually or physically, but the result will be the same.
The Benefits of Network Segmentation
While most cybersecurity experts believe that different parts of a network should be isolated from each other for better network security, very few organizations have implemented this strategy. Data from CIO reveals that even though IT experts believe that network segmentation is a crucial cybersecurity measure, less than 25 percent of organizations have implemented it.
One of the reasons why organizations are yet to make this bold step is the amount of effort required to split a network into portions properly. Professionals will need detailed information on the network infrastructure for the segments and control points to be set up without leaving gaps. The network architecture will also have to be reworked again, and this can be quite strenuous.
However, if businesses can overcome these setup challenges, many benefits can be gained from network segmentation, and they include:
Slows down Attackers
This is one of the main advantages of splitting a network into segments. When an attacker manages to breach into one segment, they will be contained into that segment for a while since the other segments are still secure.
As they try to break into other segments to access more resources, you will have time to upgrade the security of the different segments to ensure that they are not able to access vital company resources. Segmentation, therefore, buys you time in the case of an intrusion, and this limits the damage that external attacks can cause.
Improved Monitoring
It is easy to monitor the happenings on a network when it has been segmented. You can easily monitor log events and unsuccessful internal connections when the network has been partitioned into segments. From these events, you can quickly identify suspicious behavior and take the necessary measures to improve your network security.
Better Data Security
Network segmentation allows you to apply stronger security measures to the most sensitive data in your organization. Segmenting your networks will make it easy for you to add a layer of protection on your internal network assets, and this ensures that sensitive company information does not get to the wrong hands. This also minimizes the risk of losing vital company data and data theft.
It Is Easy to Implement the Least Privilege Policy

Organizations should restrict access to sensitive information systems within the organization, and network segmentation makes it possible to achieve this. A segmented network infrastructure restricts access to such vital assets to a few selected individuals, and this goes a long way to protect the company data.
If an individual’s login credentials are abused or compromised, access to the assets will be restricted, and this protects the organization from internal as well as external attacks.
The Damage from Successful Attacks Is Reduced
If an intruder manages to break into your network, he or she will only be able to access the recourses within that network segment. Network segmentation adds a layer of protection to each segment, and this means that intruders will only access the resources of the segment that they have broken into.
The other segments will be safe, and the resources within them uncompromised. The damage from successful attacks is, therefore, reduced, and this is another reason why organizations should make sure that their network infrastructure is segmented.
Conclusion
Networks are facing more threats than before, and organizations need to up their security mechanisms to avoid data loss and theft. Network segmentation is an effective cybersecurity measure that organizations need to take up to keep their systems safe and data secure.
Featured Image Credit: stack8.com
