
How Remote Management Tools Help Colocation Customers
May 28, 2020
What Has Virtualization Looked like in 2020?
June 3, 2020From the past five years, the trend of using cloud computing is increasing day-by-day because it is an on-demand IT provisioning business model focused on distributed computing technologies and virtualization. Moreover, the frameworks of cloud computing include programmatic management, flexibility, scalability, highly abstracted resources, and the numerous shared resources such as database, memory, hardware, etc.
Small to medium-sized businesses are taking huge advantage from cloud computing because it allows them to transfer an extensive range of shared posts, products, and advertising pitches freely from anywhere.
Credit: 360Logica
The modernized workspace, powerful security, round-the-clock tracking, quick backups, remote access, portability, and market productivity are some significant reasons that captivate the attention of merchants and make them confident for the migration of their services to the cloud.
A Short Introduction to Cloud Computing & Business Stats 2020
The process that helps in distributing several software and hardware services online with the help of centralized remote servers is known as cloud computing. The remote servers of the cloud provide the active data storage and maintenance facilities to make it comfortable for the users to upgrade or broaden the thousands of data into existing infrastructure.
Cloud computing is categorized into three parts:
SaaS – SaaS is the software as a service that is the sturdy software distribution model equipped by the third party providers for the users who want to run the applications online without downloading the software into personal computers. The biggest examples of SaaS are Hubspot, GoogleDocs, Web Content Delivery Services, Salesforce, Dropbox, ZenDesk, Slack, MailChimp, BigCommerce.
PaaS – The Platform as a service or Paas helps the clients build new apps by using the remote and embedded configurable APIs. Also, the service features many development tools, configuration management platforms, and frameworks for deployment. Google App Engine, Force, Microsoft Azure, Magento Commerce Cloud are the real examples of PaaS.
IaaS – IaaS is defined as the infrastructure as service, offering the abstract OS, hardware, and virtual machines that may be controlled via API services. The typical examples of IaaS are Rackspace Cloud, Amazon EC2 and S3, Windows Live Skydrive, and much more.
Cloud Adoption Statistics for 2020

Credit: gartner
- According to Gartner, it is projected that the global public cloud service market will reach nearly $266 billion in 2020. By 2022, the transition to the cloud will influence more than 1.3 dollars trillion in IT spending.
- 94% of the enterprise’s first choice is cloud now & by 2020, 83% of enterprises will place their maximum data in the cloud.
- The largest public cloud market was the US in 2019, with the maximum spending of $124.6 billion.
4 Cloud Computing Security Risks Faced by Every Business
Even after a handful of benefits, timely updates, collaborative environment, this populous cloud computing is flooded with certain security flaws that need to be understood.
Partial Data Deletion
The OS (operating systems) do not help in wiping the data accurately when the users request to delete the cloud resources. It may happen when the customers store the additional copies of data or give them access to other clients for using the cloud, but they destroy the disk. The reusability of hardware resources and the multiple agreements poses severe risks for the customers.
Before utilizing the cloud provider’s services, one must check the terms and conditions and discover the reviews if provided on the websites. Another way is to consult with web developers or cloud testers who know how to protect sensitive information from unauthorized parties.
Apart from that, you should provide limited access to subsets, company persons. Though, if you use the public cloud, the chances are very high to lose the securities. So, it would be great for you to put your data from the professionals on private cloud or demand for alternative solutions to control the future risks.
Middle Ground Management Interface
The public cloud providers’ customer management interfaces offer the freedom to access the large resource sets via the internet. This respect increases the risk factors, especially when combined with vulnerable web browsers or when masses decide to operate the service remotely.

Credit: Cubet
On one side, it proffers the ease of processing the thousands of data. On the other hand, it leaves the malware, bots, malicious bugs in a hidden manner. The cloud architecture includes high-risk functions like CP network administrators and managed security service providers that can damage your assets.
According to you, cloud computing is perfect for storing endless products, images, and videos, but you should keep the security always in mind. Before purchasing a cloud service, you should ask some questions from the service providers.
For example – Is it possible to move the operations and public data to a private cloud? Do you provide any guarantee to protect the assets with configuration management controls, vulnerability assessment, or access controls?
Noncompliance Standards
Small organizations rely heavily on cloud service providers because many providers give them access to the cloud without taking SLA agreement. In other words, you can assume that they do not have any legal policies to use the service. Due to this concern, sometimes, they do not understand how the cloud works and face integrity issues.
Before or after transferring the resources on the cloud, it is vital to perform the integration or security testing. Furthermore, you should check the reliability, performance of the service model, or consider the procedures or SLA agreements to overcome the insecurity issues.
DDoS (Distributed Denial of Service) Attacks
There is no doubt that the cloud allows consumers to save a wide array of data, but it entirely works with the internet connection. During connectivity, occasionally, cyberattacks and malware infection like activities happen with the cloud services.
It is one of the significant threats faced by the vendors as the information of the businesses is stolen by the hackers who send unprecedented traffic volume to the web-based applications. The servers crashing occur with these web connectivity attacks.
First of all, the DDoS attacks originate with the single Ip addresses so you can get the configuration of your networks from the engineers and ask them to block the DNS responses that are coming from the outside connections. You can increase the bandwidth or move your solution in cloud-based DNS that may offer the data centers with the multiple points of presence as well as take care of the load balancing.
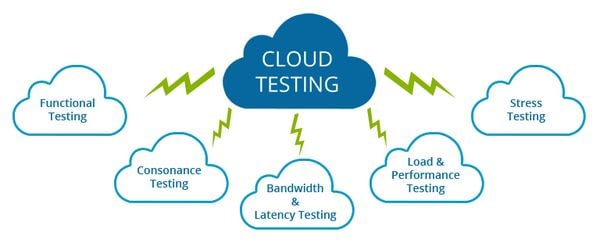
Overcome the Cloud Computing Business Threats with Cloud Testing
Cloud testing is the only key to address the security problems of a cloud-based environment. It is the kind of software testing that uses real-world web traffic for removing the bugs from the cloud computing services. Cloud testing focuses on three main core components that are infrastructure, network, and application.
Testing the application over the cloud provides the multitenancy, interoperability, disaster recovery, on-demand self-service, rapid elasticity, broad network access, resource pooling, and abundance of protection against crashing and data loss. Before or After selecting the right cloud provider, the organizations should consider the cloud-based automation testing or cloud-based security testing for its applications on the cloud.
It not only reduces the risks of data outages but also provides several types of testing that are mentioned below:
Performance Testing
With performance testing, it is easy to monitor the stability of software programs, computers, networks, responsiveness under a particular workload.
Functional/Non-Functional Testing
The automated functional testing allows cloud testers to record the open-source scripts from the cloud and is the valuable software testing for checking the functionality of Login. On the other hand, non-functional testing is beneficial for improving usability and loading performance.
Load Testing
If you have given your cloud access to multiple users and want to determine the application’s behavior after containing heavy stuff, you should test the virtual machines with the cloud load testing from the personnel. They will inform you whenever there is a need to increase the bandwidth or storage in a cloud.
Major Benefits of Using the Cloud Testing
Disaster Recovery
The disaster recovery testing is the step-by-step practice of a disaster recovery plan that is mainly designed for companies who want to restore their IT system after the event of failure.
ROI & Cost Savings
Any person who adopts the cloud services can migrate the data to remotely located data centers. Cloud testing helps to achieve a faster ROI by minimizing the cost of infrastructure equipment management.
Dynamic & Readily Available Environment
The cloud computing testing offers dynamic operations with an on-demand service to test the application with quick turnaround time. Any cloud testing application, which runs with the subscription model, can bring enormous benefits after making the successful registration on the browsers.
Getting first-class security on the cloud with testing should be your prime responsibility. It gives sufficient support to fix the number of issues at the most cost-effective prices and offers you unlimited availability of resources, multi-factor authentication, confidentiality, and much more.
Main Photo Credit: David Tzemach’s Blog

1 Comment
Cloud-based testing has risen as a new and cost-effective strategy for software testing, and the increasing significance of cloud testing has gained recognition in recent years. Yes, cloud testing has a splendid future with the potential to transform the way software testing does execute, and it aims to reduce testing costs significantly.
Also, cloud testing has given rise to a slew of cloud-based testing tools in the market, and it has given rise to TaaS (Testing as a Service), which allows firms to outsource their testing purposes.